The Challenge #
When you go to the instance, you’ll see a web page with a random string that needs to be MD5 hashed.
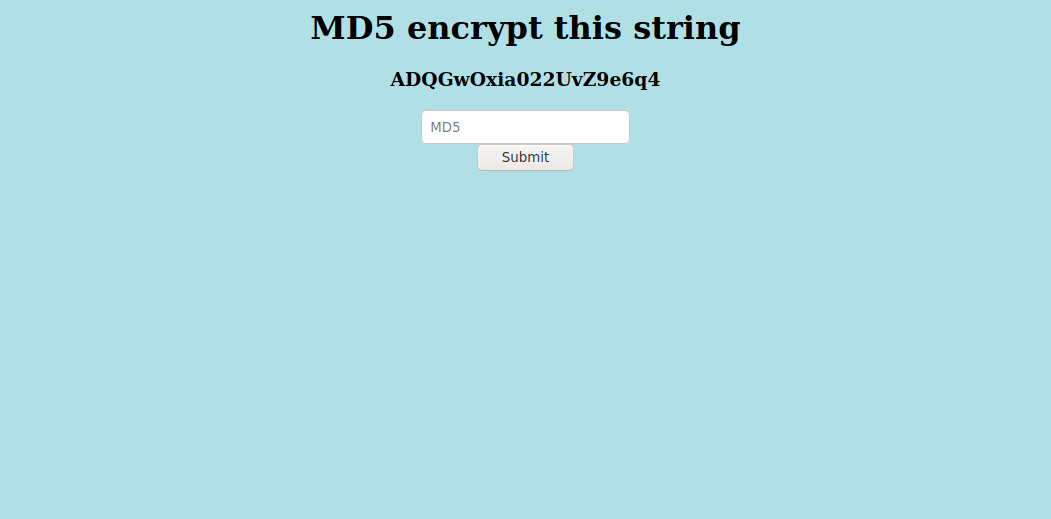
At first glance, this seems like a very simple task:
- Copy the string
- MD5 Hash the string
- Submit the result
echo -n 'ADQGwOxia022UvZ9e6q4' | md5sum
6f1fdaa71690ea243344374cfab2b977 -
Submit the hash into the website!
Getting a Little Faster #
You can try to speed this up a bit by using pbpaste and pbcopy (if you’re on a Mac).
If you happen to be on a Linux machine, alias those commands as the following:
alias pbcopy='xclip -selection clipboard'
alias pbpaste='xclip -selection clipboard -o'
To make this a quicker one liner:
pbpaste | md5sum | cut -d' ' -f1 | pbcopy
Let’s try again:
- Refresh the page
- Alt+Tab to your terminal
- Run command
- Alt+Tab to Firefox
- Submit

No dice! Back to the drawing board
Scripting #
Looks like we’ll have to get our hands dirty with some scripting. I’m a fan of utilizing command line utilities, so I decided to write a bash script.
Bash Script #
The first problem that needs to be solved is obtaining the current string to hash.
Viewing the source on the website, using curl, you can see that the string-to-be-hashed will always be on the 6th line.
We can grab the line using head and tail.
curl -s http://159.65.92.160:31460 | head -n 6 | tail -n1
<h1 align='center'>MD5 encrypt this string</h1><h3 align='center'>R58rJ7KvvsqV7mCiUWhH</h3><center><form action="" method="post">
Looking good!
I know there’s a way to extract the hash using a regex, but I went for using cut on the < and > characters.
Then use tr to remove the newline character from the end of the input.
If the newline character isn’t removed, the MD5 hash will be wrong!
To use cut and tr, append cut -d '>' -f 4 | cut -d '<' -f1 | tr -d '\n'.
The new command looks like:
curl -s http://159.65.92.160:31460 | head -n 6 | tail -n1 | cut -d '>' -f 4 | cut -d '<' -f1 | tr -d '\n'
v0KsOyOCpiMyOI5sVxET
Now that can be passed to md5sum and extract the hash, and save it to a variable $hash in the shell script.
We can also make a local variable $HOST for the URL.
The beginning of the bash script looks like this:
#!/usr/bin/env bash
# change this to your instance IP:PORT
HOST=http://159.65.87.50:32540/
hash=$(curl -s $HOST | head -n 6 | tail -n1 | cut -d '>' -f 4 | cut -d '<' -f1 | tr -d '\n' | md5sum | cut -d' ' -f1)
The only thing that’s left is to submit the MD5 hash to the web app.
Again, we can use curl to submit the result.
To figure out how the form works, open your browser’s developer tools, and go to networking tab.
Remove all the data that’s there, enter in a fake hash, and click submit.
Find the POST to / and inspect the request.
Notice how there’s one variable called hash, and the headers of the request has a Content-Type of application/x-www-form-urlencoded.
Using all this new knowledge, we can build a curl command to submit the hash.
curl -X POST \
-H 'Content-Type: application/x-www-form-urlencoded' \
--data "hash=$hash" \
$HOST
Combined with what we had before, the script:
#!/usr/bin/env bash
# change this to your instance IP:PORT
HOST=http://159.65.87.50:32540/
hash=$(curl -s $HOST | head -n 6 | tail -n1 | cut -d '>' -f 4 | cut -d '<' -f1 | tr -d '\n' | md5sum | cut -d' ' -f1);
curl -X POST \
-H 'Content-Type: application/x-www-form-urlencoded' \
--data "hash=$hash" \
$HOST
Run the script again and let’s get that flag!

So close! The web page still says Too slow!.
Why this Failed #
TL;DR -> cookies
Reinspecting the headers, there’s a PHPSESSIONID cookie that is set.
But fear not!
This can easily be applied to the curl commands.
To set save a cookie, use the -c flag in the command with a name of the jar.
To load a cookie, use the -b flag with the name of the jar.
This is a small fix in the current script.
Keeping things simple, call the cookie file cookie.txt.
The final piece I like to add is grep -oh -E 'HTB{(.*)}'.
This grep command, only displays the matched string (without the filename) and looks for a regex of the Hack the Box flag.
Cleans up the output a bit.
#!/usr/bin/env bash
# change this to your instance IP:PORT
HOST=http://159.65.87.50:32540/
hash=$(curl -c 'cookie.txt' -s $HOST | head -n 6 | tail -n1 | cut -d '>' -f 4 | cut -d '<' -f1 | tr -d '\n' | md5sum | cut -d' ' -f1);
curl -s \
-X POST \
-b 'cookie.txt' \
-H 'Content-Type: application/x-www-form-urlencoded' \
--data "hash=$hash" \
$HOST \
| grep -oh -E 'HTB{(.*)}'
Conclusion #
I found this challenge to be easy, but fun. I really enjoy getting into scripting and making my own solutions to these kinds of problems. Don’t like bash or go? Feel free to translate these solutions into the language of your choice! Challenges like these really make me get back to my roots with Linux and re-solidify the plethora of amazing command line tools that are available and how they can be chained together to produce something incredible. I hope you enjoyed this walk-through and learned something new!
👋 じゃまった

